WikiDevi.Wi-Cat.RU:DD-WRT/Separate LAN and WLAN
Introduction
This guide explains how to separate the wireless interface from the "LAN&WLAN" bridge so that they are on different subnets. You are then able to control communication between the interfaces using iptables commands.
If your router is configured as a Wireless Access Point (WAN is disabled) then you must be sure to set the gateway and local DNS as recommended in the WAP guide. This also applies to WDS client nodes (but not the main WDS node) which are bridged to another router that does routing for them. Keep your eye out for the places this guide gives alternative instructions for WAP's.
Note: If you're separating virtual interfaces then use the instructions from the Multiple WLAN Guide.
Preparation
Go to the Administration -> Commands page, insert the command below, and press the Run Commands button to find out the actual name of your wl0 interface. If you have a wl1 interface that you want to unbridge then change the command accordingly.
nvram get wl0_ifname
Before beginning, read Bug 1853 about a minor bug with bridge creation and a haphazard fix to the bug that was introduced in changeset 16181. This guide will NOT be changed to reflect the bridge creation changes until recommended builds are affected by the change.
Configuration
Step 1: Remove the Wireless Interface from the LAN bridge
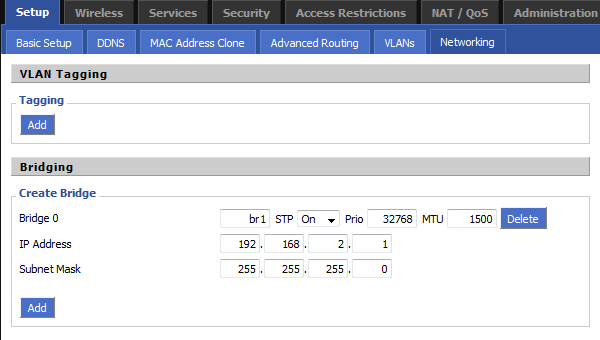
- Navigate to the Setup -> Networking page.
- Press the Add button in the Create Bridge section
- Type "br1" into the blank input box that is on the left side of all the options that just appeared.
- Press the Apply Settings button at the bottom of the page and new input boxes will appear.
- Set an IP Address that is in an unused subnet. ie. 192.168.2.1
- Set the Subnet Mask to 255.255.255.0
- Press the Apply Settings button again so that the IP address will be assigned to the br1 interface before you continue.
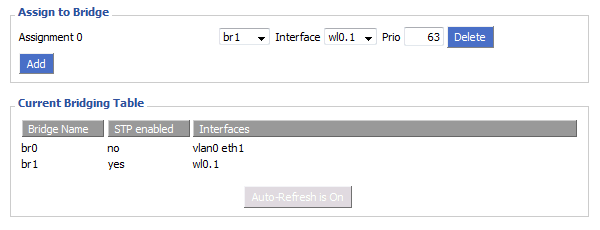
- Press the Add button in the Assign to Bridge section.
- Select br1 in the left drop down menu that appeared and in the middle menu select the name of your wireless interface that you discovered during the preparation.
- Press the Apply Settings button and the wireless interface will now be moved from br0 to br1.
Note: The picture below displays a virtual wireless interface being assigned to br1 instead of the physical interface. Be sure to assign your physical interface as instructed already.
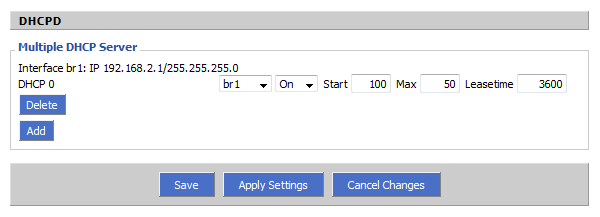
Step 2: Add DHCP for the unbridged WLAN interface
- Press the Add button in the Multiple DHCP Server section.
- Select br1 in the left drop down menu that appeared.
- Press the Apply Settings button to finish enabling the DHCP server for the wireless interface.
If DHCP is disabled on your main LAN in Basic Setup, then the Multiple DHCP method above will not work. Instead you will need to use Additional DNSMasq Options.
Go to the Services tab and find the DNSMasq section. Make sure that DNSMasq is Enabled. Adjust the following options to fit your environment (omit the comment lines starting with '#') and them to the Additional DNSMasq Options text area.
# Enables DHCP on br1 interface=br1 # Set the default gateway for br1 clients dhcp-option=br1,3,192.168.2.1 # Set the DHCP range and default lease time of 24 hours for br1 clients dhcp-range=br1,192.168.2.100,192.168.2.150,255.255.255.0,24h
If you would like to use different DNS servers for the VAP then you can use this DNSMasq option regardless of which DHCP configuration method you used.
dhcp-option=br1,6,[DNS IP 1],[DNS IP 2]
You should now be able to connect to the unbridged wireless interface and receive a DHCP lease with an IP address that is in the 192.168.2.0/24 subnet. Make sure that you can connect to it, receive a DHCP lease, and connect to the router's 192.168.2.1 address before you do anything further. If your WAN port is active (ie. you're not making a WAP) then you should also be able to browse the internet. If you are making a WAP then you must either use the iptables commands for WAP's in the next section, or create routes throughout your network.
Step 3: Controlling Access
Now that you have your WLAN separated you can start limiting what access it has. Here are several iptables commands that you can save to your firewall script on the Administration -> Commands page. These commands are written in the same order that the should appear in your firewall script, changing the order can affect the way that they work. Mix and match them however you like, just be sure to keep them in the order they appear on this page.
If you have any problems with your firewall script, then create a forum thread and be sure to describe in great detail what you're trying to do, what it is actually doing, and post your firewall script.
Enable NAT on the WAN port to correct a bug in builds over 17000
iptables -t nat -I POSTROUTING -o `get_wanface` -j SNAT --to `nvram get wan_ipaddr`
Allow br1 access to br0, the WAN, and any other subnets (required if SPI firewall is on)
iptables -I FORWARD -i br1 -m state --state NEW -j ACCEPT iptables -I FORWARD -p tcp --tcp-flags SYN,RST SYN -j TCPMSS --clamp-mss-to-pmtu
Restrict br1 from accessing br0 (do not use on WAP's)
iptables -I FORWARD -i br1 -o br0 -m state --state NEW -j DROP
Restrict br0 from accessing br1
iptables -I FORWARD -i br0 -o br1 -m state --state NEW -j DROP
Restrict br1 from accessing the WAN port (no internet access!)
iptables -I FORWARD -i br1 -o `get_wanface` -j DROP
Restrict br1 from accessing the WAN subnet (still has internet, do not use on WAPs)
iptables -I FORWARD -i br1 -d `nvram get wan_ipaddr`/`nvram get wan_netmask` -m state --state NEW -j DROP
Restrict br1 from accessing br0's subnet but pass traffic through br0 to the internet (for WAP's - WAN port disabled)
iptables -I FORWARD -i br1 -d `nvram get lan_ipaddr`/`nvram get lan_netmask` -m state --state NEW -j DROP
Enable NAT for traffic being routed out br0 so that br1 has connectivity (for WAP's - WAN port disabled)
iptables -t nat -I POSTROUTING -o br0 -j SNAT --to `nvram get lan_ipaddr`
Restrict br1 from accessing the router's local sockets (software running on the router)
iptables -I INPUT -i br1 -m state --state NEW -j DROP
Allow br1 to access DHCP on the router
iptables -I INPUT -i br1 -p udp --dport 67 -j ACCEPT
Allow br1 to access DNS on the router
iptables -I INPUT -i br1 -p udp --dport 53 -j ACCEPT iptables -I INPUT -i br1 -p tcp --dport 53 -j ACCEPT
References
- V24: WLAN separate from LAN, with independent DHCP - A similar guide
- WLAN separate from LAN, with independent dhcp, etc - Command line method (old)
- Multiple WLANs - For unbridging virtual wireless interfaces